The dark web has evolved from a mysterious corner of the internet into a thriving ecosystem where stolen data, login credentials, intellectual property, and sensitive corporate information are bought and sold every day. For businesses and individuals alike, this underground marketplace presents a very real risk. That’s where dark web monitoring tools with real-time alerts come in—powerful solutions designed to detect compromised data the moment it appears and enable rapid response before damage escalates.
TLDR: Dark web monitoring tools scan hidden forums, marketplaces, and data dumps to detect exposed credentials and sensitive information. The most advanced platforms offer real-time alerts, AI-driven analysis, and automated response tools to reduce damage quickly. These tools are essential for preventing identity theft, data breaches, financial fraud, and brand harm. Investing in proactive monitoring is far less costly than recovering from a breach.
Modern cybercrime moves fast. When employee credentials or customer data land on the dark web, attackers waste no time exploiting it. The difference between a minor incident and a full-scale breach often comes down to speed of detection. Real-time dark web monitoring tools are specifically built to close that gap.
What Is Dark Web Monitoring?
The dark web is a portion of the internet that requires specialized software, such as Tor, to access. It hosts anonymous marketplaces, encrypted forums, and illicit trading networks. While not everything on the dark web is illegal, it has become a central hub for cybercriminal activity.
Dark web monitoring involves continuously scanning:
- Hidden forums
- Black market marketplaces
- Paste sites
- Encrypted chat channels
- Leaked credential dumps
- Ransomware leak sites
Monitoring tools collect and analyze this data, searching for stolen usernames, passwords, credit card numbers, Social Security numbers, intellectual property, and brand mentions.

Why Real-Time Alerts Matter
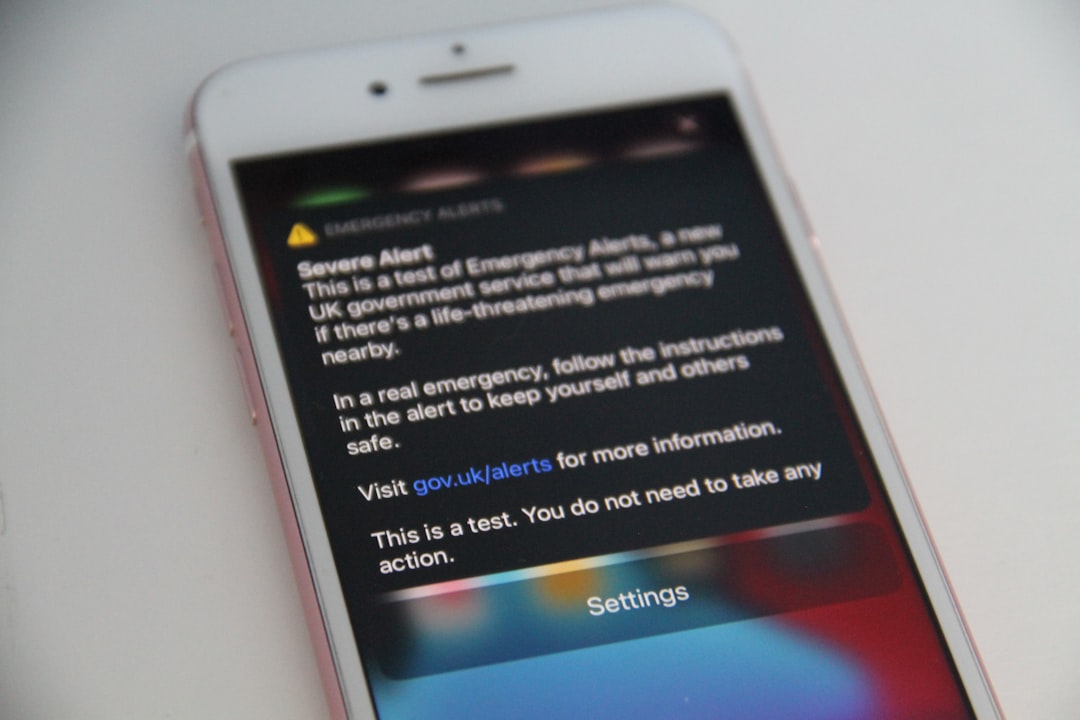
Not all dark web monitoring tools operate at the same speed. Older systems might scan periodically and generate delayed reports. However, today’s threat landscape demands instant awareness.
Imagine an employee’s corporate login credentials appear in a leaked database. Within hours, attackers may attempt credential stuffing attacks across business systems. A real-time alert allows security teams to:
- Immediately reset compromised passwords
- Disable exposed accounts
- Initiate multi-factor authentication enforcement
- Investigate for unauthorized access
- Notify affected individuals quickly
The faster the response, the less severe the consequences. In cybersecurity, minutes matter.
Core Features of Dark Web Monitoring Tools
Modern solutions combine automation, machine learning, and threat intelligence feeds to deliver actionable insights. Leading dark web monitoring platforms typically include:
1. Continuous Crawling and Data Collection
Automated bots crawl hidden networks 24/7, indexing forums, marketplaces, and chat rooms that would otherwise be inaccessible.
2. AI-Powered Pattern Recognition
Machine learning models analyze massive datasets to identify compromised credentials, brand mentions, or sensitive corporate data. Advanced AI reduces false positives and highlights legitimate threats.
3. Customizable Alert Systems
Organizations can configure triggers based on:
- Specific employee email domains
- Executive names
- Customer databases
- Intellectual property keywords
- Financial account identifiers
4. Real-Time Notifications
Alerts can be delivered through:
- Email notifications
- SMS messages
- SIEM integrations
- Slack or collaboration tools
- API integrations into security platforms
5. Forensic Context
High-quality tools don’t just issue alerts—they provide context. This may include screenshots of the listing, timestamps, source links, and risk scoring to prioritize responses.
Who Needs Dark Web Monitoring?
Contrary to popular belief, dark web risks aren’t limited to large enterprises. A wide range of users benefit from monitoring tools:
Businesses and Enterprises
Businesses face risks including:
- Credential leaks
- Corporate espionage
- Ransomware disclosures
- Data breach reputational damage
For companies, dark web monitoring is often integrated into a broader threat intelligence strategy.
Small and Medium-Sized Businesses (SMBs)
SMBs are frequent targets because they often lack advanced security resources. Real-time alerts help them act quickly even with smaller IT teams.
Individuals and Executives
High-net-worth individuals, executives, and public figures are prime targets for identity theft, phishing campaigns, and impersonation schemes. Monitoring services can alert them if personal credentials surface in malicious forums.
Financial Institutions
Banks and fintech companies use monitoring to detect stolen account information or card data circulating on black markets before fraud escalates.
How Real-Time Monitoring Prevents Damage
The benefits of early detection go beyond simple awareness. Real-time dark web monitoring supports multiple forms of damage prevention:
Fraud Prevention
By identifying compromised credit card data immediately, institutions can freeze accounts before transactions occur.
Ransomware Mitigation
Many ransomware groups publish stolen data on leak sites. Monitoring tools can notify companies when their name appears—sometimes even before attackers initiate direct contact.
Brand Protection
Fake domains, impersonation accounts, or counterfeit product listings can damage brand trust. Monitoring allows marketing and legal teams to act rapidly.
Credential Protection
Password reuse remains common. If employee logins are found in a breach dump unrelated to your organization, proactive resets can prevent account takeover attempts.
Key Considerations When Choosing a Tool
With numerous vendors on the market, selecting the right dark web monitoring solution requires careful evaluation.
Coverage Depth
Does the tool monitor only surface-level forums, or does it reach deep hidden Tor networks and encrypted spaces?
Alert Speed
Is the platform truly real-time, or does it operate on delayed batch scans?
Accuracy and False Positives
High volumes of irrelevant alerts can overwhelm security teams. Look for AI filtering and contextual analysis.
Integration Capabilities
Seamless integration with existing security infrastructure—such as SIEM, SOAR, and identity management systems—improves response efficiency.
Compliance Support
For regulated industries, monitoring can support compliance requirements under GDPR, HIPAA, PCI-DSS, and other frameworks by demonstrating proactive breach detection efforts.
The Role of Automation and AI
The sheer scale of dark web data makes manual monitoring impossible. Automation is now central to effective scanning and analysis.
Advanced tools leverage:
- Natural language processing (NLP) to interpret multilingual posts
- Image recognition to analyze screenshots of stolen databases
- Behavioral analytics to identify suspicious seller patterns
- Risk scoring models to prioritize threats
This technology allows security teams to focus on strategy and response rather than raw data parsing.
Common Limitations and Misconceptions
Despite their power, dark web monitoring tools are not magic solutions.
They cannot:
- Prevent all data breaches
- Access every single private encrypted conversation
- Guarantee 100% visibility into new hidden sites
They are most effective when combined with other cybersecurity practices, such as:
- Zero-trust architecture
- Multi-factor authentication
- Endpoint detection and response
- Regular security awareness training
Monitoring is a detection and intelligence layer—not a full security replacement.
The Future of Dark Web Monitoring
Cybercriminals continue to evolve, adopting new encrypted communication platforms and decentralized marketplaces. In response, monitoring tools are becoming more sophisticated.
Future developments may include:
- Predictive threat modeling
- Deeper integration with automated incident response systems
- Real-time takedown collaboration with law enforcement
- Expanded monitoring into emerging anonymous networks
We can also expect stronger use of artificial intelligence to map criminal ecosystems and identify patterns before large-scale attacks unfold.
Final Thoughts
In today’s hyperconnected digital landscape, the dark web represents both an intelligence goldmine and a significant threat vector. Organizations that lack visibility into this hidden world operate at a disadvantage. Dark web monitoring tools with real-time alerts provide that visibility—transforming secrecy into actionable intelligence.
By enabling early detection of compromised credentials, leaked data, and brand threats, these tools buy something incredibly valuable: time. And in cybersecurity, time often determines whether an incident becomes a minor inconvenience or a catastrophic event.
Proactive monitoring is no longer optional for organizations serious about protecting their data, reputation, and customers. The dark web may remain hidden—but with the right tools, its risks don’t have to remain invisible.
