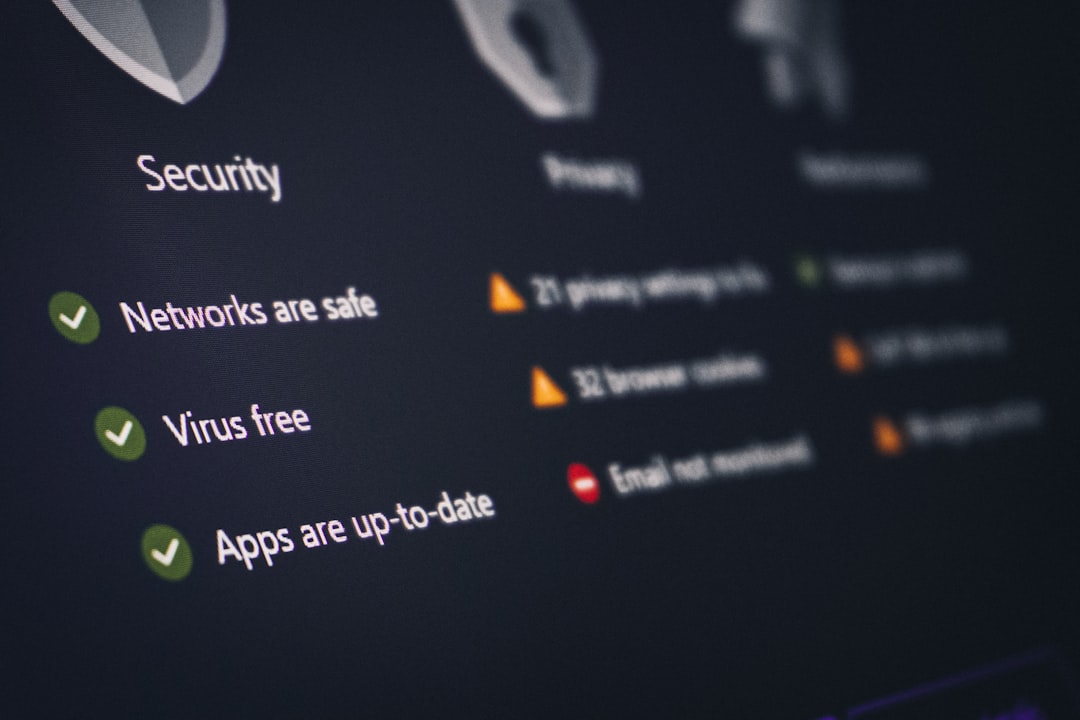
Modern cyberattacks move fast, evade traditional defenses, and often bypass signature-based antivirus solutions entirely. As organizations embrace cloud infrastructure, hybrid work, and SaaS ecosystems, endpoint security has become a critical control point. This is where Endpoint Detection and Response (EDR) platforms come in—providing continuous monitoring, behavioral detection, threat intelligence, and rapid containment capabilities to stop attacks before they escalate.
TLDR: Endpoint Detection and Response (EDR) tools help organizations identify, investigate, and neutralize threats in real time. While CrowdStrike Falcon is a market leader, several other powerful EDR platforms offer comparable capabilities, including advanced analytics, threat intelligence, and automated remediation. This article explores six trusted alternatives and compares their strengths, features, and ideal use cases. Choosing the right solution depends on your organization’s size, infrastructure, and security maturity.
Below are six reputable EDR tools like CrowdStrike Falcon that security teams rely on to detect and respond to modern threats effectively.
1. Microsoft Defender for Endpoint
Microsoft Defender for Endpoint has evolved into a comprehensive enterprise EDR solution. Deeply integrated with the Microsoft ecosystem, it provides behavioral threat detection, attack surface reduction, vulnerability management, and automated investigation capabilities.
One of its strongest advantages is seamless integration with Microsoft 365, Azure AD, and Microsoft Sentinel, making it particularly powerful for organizations already invested in Microsoft infrastructure.
Key Features:
- Behavioral-based detection and AI-driven analytics
- Automated investigation and remediation (AIR)
- Threat and vulnerability management
- Integration with SIEM and XDR tools
- Cross-platform support (Windows, macOS, Linux, mobile)
Best For: Enterprises operating heavily in Microsoft environments seeking tight ecosystem integration.
2. SentinelOne Singularity Endpoint
SentinelOne Singularity is a well-known AI-powered endpoint security platform that competes directly with CrowdStrike. It combines EDR, XDR, and automated response capabilities into a unified agent.
Its autonomous remediation capabilities stand out. The platform can automatically roll back malicious changes using patented snapshot technology, reducing the need for manual incident response.
Key Features:
- AI-driven behavioral detection
- Automated remediation and rollback
- Ransomware protection
- Cloud-native architecture
- Device control and firewall management
Best For: Organizations seeking high automation and reduced reliance on manual investigation.
3. Sophos Intercept X with EDR
Sophos Intercept X combines powerful endpoint protection with extended detection and response capabilities. It is widely respected for its strong anti-ransomware defenses and exploit prevention mechanisms.
The platform provides actionable threat intelligence and root cause analysis, allowing security teams to trace attacks from initial compromise to lateral movement.
Key Features:
- Deep learning malware detection
- CryptoGuard anti-ransomware technology
- Root cause analysis visualization
- Managed Threat Response (MTR) option
- Synchronized security with Sophos Firewall
Best For: Mid-sized organizations looking for strong ransomware protection and optional managed detection services.
4. Trend Micro Apex One with EDR
Trend Micro Apex One delivers a blend of traditional endpoint protection and advanced EDR capabilities. It uses behavioral analysis, machine learning, and threat intelligence to protect endpoints against both known and unknown threats.
Trend Micro’s strength lies in its global threat intelligence network, which continuously feeds real-time threat data into the platform.
Key Features:
- Behavior monitoring and exploit prevention
- High-fidelity threat detection
- Integrated EDR and XDR options
- Application control and device control
- Centralized management console
Best For: Enterprises seeking layered endpoint protection backed by global threat intelligence.
5. VMware Carbon Black Cloud
VMware Carbon Black Cloud offers cloud-native endpoint protection designed for modern enterprise environments. It is particularly strong in behavioral EDR and threat hunting.
Carbon Black provides continuous endpoint recording, giving security teams granular visibility into endpoint activity. This is particularly useful during forensic investigations.
Key Features:
- Continuous endpoint activity monitoring
- Behavioral detection and threat hunting
- Cloud-native architecture
- Workload protection for virtual environments
- Integration with VMware ecosystem
Best For: Organizations using VMware infrastructure or requiring deep forensic capabilities.
6. Palo Alto Networks Cortex XDR
Cortex XDR extends beyond traditional EDR by combining endpoint, network, and cloud telemetry into a unified detection and response system. While it includes strong endpoint protection, its true power is correlation across data sources.
This broader context reduces alert fatigue and improves detection accuracy by correlating related events into prioritized incidents.
Key Features:
- Cross-data analytics across endpoint, network, and cloud
- Machine learning-based detection
- Automated root cause analysis
- Threat intelligence integration
- Managed detection and response (MDR) options
Best For: Large enterprises looking for XDR-level visibility beyond endpoints alone.

Feature Comparison Chart
| Tool | AI Driven Detection | Automated Remediation | Ransomware Protection | Cloud Native | Best For |
|---|---|---|---|---|---|
| Microsoft Defender | Yes | Yes | Strong | Yes | Microsoft-focused enterprises |
| SentinelOne | Yes | Advanced rollback | Excellent | Yes | Automation-focused teams |
| Sophos Intercept X | Yes | Yes | Excellent | Partial | Mid-size businesses |
| Trend Micro Apex One | Yes | Limited | Strong | Hybrid | Layered enterprise security |
| VMware Carbon Black | Yes | Partial | Good | Yes | VMware environments |
| Cortex XDR | Yes | Advanced | Strong | Yes | Large enterprises, XDR adoption |
How to Choose the Right EDR Tool
Selecting the right EDR solution is not simply about feature checklists. It requires a realistic assessment of your organization’s threat landscape, internal expertise, and infrastructure complexity.
Consider the Following:
- Integration: Does the tool align with your existing ecosystem (Microsoft, VMware, Palo Alto)?
- Automation: Do you need autonomous remediation, or does your SOC prefer manual control?
- Scalability: Can it handle growth in endpoints and cloud workloads?
- Threat Intelligence: Is global threat intelligence included?
- Managed Services: Does the vendor offer MDR if in-house resources are limited?
Organizations with mature security teams may prioritize visibility and hunt capabilities, while leaner teams may prefer platforms with strong automation and managed services.
Final Thoughts
Endpoint Detection and Response has become a foundational layer of modern cybersecurity strategy. Threat actors increasingly exploit endpoints through phishing, ransomware, credential theft, and zero-day exploits. Without continuous monitoring and rapid containment capabilities, traditional antivirus solutions are insufficient.
While CrowdStrike Falcon remains a benchmark in the EDR market, the alternatives discussed here provide serious, enterprise-grade protection. Microsoft Defender delivers powerful ecosystem integration. SentinelOne excels in automation. Sophos focuses on ransomware resilience. Trend Micro offers layered intelligence-driven security. VMware Carbon Black shines in deep visibility. Cortex XDR expands detection across the enterprise.
The most effective choice depends on your operational needs, security maturity, and infrastructure profile. What remains clear is that investing in a robust EDR platform is no longer optional—it is an essential defense against today’s rapidly evolving threat landscape.
