Language shapes perception, and perception shapes reality. Few terms illustrate this dynamic better than Cbybxrf—a word that, while obscure at first glance, carries layered meaning depending on context, culture, and interpretation. Whether encountered in digital spaces, theoretical discourse, or coded communication, Cbybxrf invites analysis beyond surface-level recognition.
TLDR: Cbybxrf is a complex and context-dependent term whose meaning shifts based on linguistic framing, symbolic use, and cultural interpretation. Though it may appear cryptic, its connotation often reflects broader themes such as abstraction, coded language, and evolving communication norms. Understanding Cbybxrf requires examining its structure, usage environments, and practical implications. This article explores its connotation, provides detailed exegesis, and evaluates its relevance in real-world settings.
Understanding the Connotation of Cbybxrf
At first sight, Cbybxrf appears structurally irregular. It does not map neatly onto recognizable phonetic or semantic systems in common English usage. This visual ambiguity contributes significantly to its connotation. Words that resist immediate comprehension often acquire symbolic weight, suggesting:
- Encrypted communication
- Digital-era abstraction
- Insider knowledge or exclusivity
- Artificial or algorithmic origin
The connotation of Cbybxrf is therefore less about literal meaning and more about perceived intentional complexity. It may evoke curiosity, skepticism, or authority depending on context. In professional environments, such a term might be interpreted as technical or proprietary. In online communities, it can imply coding, alternate identities, or cryptographic play.
This layered ambiguity makes Cbybxrf a linguistic mirror—it reflects the assumptions of the audience engaging with it.
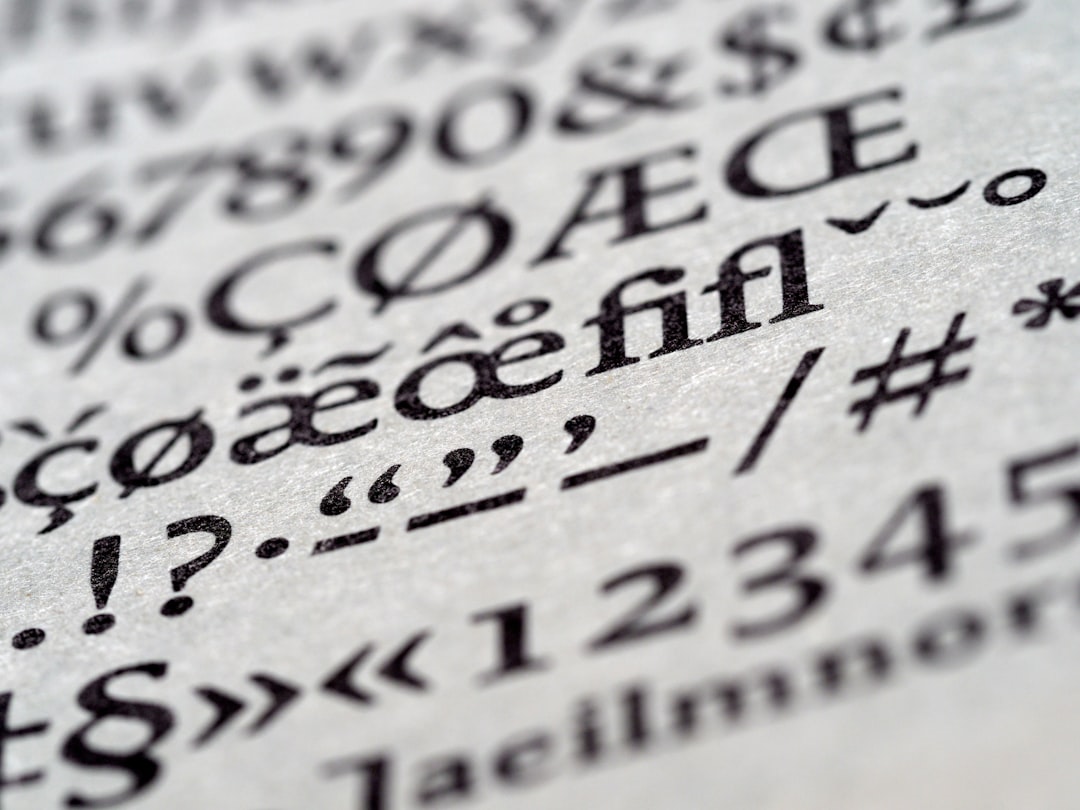
Etymological and Structural Exegesis
Although Cbybxrf does not stem from established lexical roots, its structure invites examination through several analytical lenses:
1. Phonetic Consideration
The consonant-heavy construction restricts smooth pronunciation. Limited vowel distribution interrupts natural speech rhythm, reinforcing the impression of:
- Artificial generation
- System-based creation
- Encapsulation of data rather than narrative
2. Cryptographic Interpretation
One plausible exegesis interprets Cbybxrf as a cipher-based construction. In this context, the term represents:
- A shifted alphabet pattern
- A placeholder for concealed information
- An encoded representation of another phrase
This interpretation strengthens associations with cybersecurity, algorithmic transformation, or controlled-access communication.
3. Semiotic Evaluation
From a semiotic standpoint, Cbybxrf operates as a signifier without a stable signified. The absence of widely agreed meaning forces audiences to generate interpretation through context rather than definition. In doing so, it becomes an example of how meaning is constructed socially rather than inherently.
Use of Cbybxrf in Contemporary Contexts
The practical use of Cbybxrf depends entirely on its communicative environment. Though not widely institutionalized, similar constructs appear in multiple domains.
Digital Spaces
In online environments, unconventional strings like Cbybxrf often function as:
- Usernames or identifiers designed to ensure uniqueness
- Temporary project titles awaiting final naming
- Placeholder tokens within development workflows
- Access keys or system-generated passwords
Such use imbues the term with technological legitimacy. Even when randomly generated, repeated contextual exposure can grant symbolic authority.
Academic and Conceptual Use
In theoretical discourse, an undefined term like Cbybxrf may be employed intentionally as a neutral marker—a conceptual container free from preexisting associations. This enables structured experimentation in:
- Logic modeling
- Language theory
- Information science
- Philosophy of symbols
In this setting, its neutrality becomes strength rather than limitation.
Organizational Environments
Corporations occasionally assign provisional names to confidential initiatives. Terms such as Cbybxrf can:
- Protect strategic secrecy
- Prevent premature speculation
- Create a controlled internal reference system
Once disclosed, such placeholders sometimes transition into permanent branding—demonstrating how arbitrary constructions can evolve into recognized identifiers.
Psychological Dimensions
The human response to ambiguous language is psychologically revealing. When confronted with Cbybxrf, individuals tend to:
- Attempt pattern recognition
- Assume hidden meaning
- Attribute intentional design
- Project contextual expectations
This cognitive tendency aligns with apophenia—the impulse to perceive patterns within randomness. The more structured a term appears, the stronger the assumption that it carries purpose.
Image not found in postmetaIn strategic communication, ambiguity can therefore be a deliberate tool. By presenting information that feels coded, communicators can:
- Encourage deeper engagement
- Signal exclusivity
- Enhance perceived sophistication
- Create layered audience segmentation
Real-Life Applications
Although Cbybxrf may not be commonly recognized as a standardized concept, its structural type appears regularly in everyday practice.
1. Cybersecurity
Complex strings analogous to Cbybxrf are crucial in digital protection systems. Randomized keys reduce predictability, enhancing security architecture.
2. Artificial Intelligence Systems
Machine-generated identifiers often resemble Cbybxrf formations. These identifiers:
- Label neural network parameters
- Tag datasets
- Organize algorithm iterations
3. Branding Development
While most successful brands favor pronounceability, early-stage development frequently begins with abstract placeholders. This stage allows unbiased evaluation before semantic anchoring occurs.
4. Experimental Linguistics
Researchers testing linguistic acquisition sometimes introduce unfamiliar terms to measure learning adaptability. A word like Cbybxrf serves as a controlled stimulus lacking prior associations.
Comparative Analysis of Similar Constructs
The structured randomness of Cbybxrf aligns with broader categories of coded or abstract identifiers. The following chart provides a simplified comparison:
| Construct Type | Primary Purpose | Human Readability | Semantic Meaning |
|---|---|---|---|
| Random String (e.g., Cbybxrf) | Identifier or placeholder | Low | Context dependent |
| Encrypted Code | Secure communication | Restricted | Deliberately concealed |
| Technical Acronym | Efficiency in communication | Medium to high | Defined within field |
| Branded Neologism | Market identity | High (after adoption) | Constructed, culturally shaped |
The table clarifies that Cbybxrf most closely resembles the first category: a context-sensitive identifier whose meaning emerges from usage rather than intrinsic design.
The Evolution of Meaning
Language history demonstrates that many initially incomprehensible terms later gain legitimacy. Technical vocabulary, internet slang, and brand names often begin as obscure constructs. Over time, repetition and social reinforcement stabilize interpretation.
If Cbybxrf were consistently applied within a defined context—say, a software protocol or research framework—it could follow this evolutionary pattern:
- Introduction as a neutral term
- Association with a specific function
- Repetition across users and documents
- Normalization through familiarity
- Institutionalization in formal discourse
This process illustrates an essential truth: meaning is not fixed at origin. It is constructed through sustained application.
Risks and Limitations
Despite its potential utility, reliance on abstract constructs like Cbybxrf presents certain risks:
- Misinterpretation due to lack of clarity
- Reduced accessibility for broader audiences
- Impression of unnecessary opacity
- Barrier to cross-disciplinary understanding
For this reason, deliberate context-setting is essential whenever such terms are used in formal writing or communication.
Conclusion
Cbybxrf stands as a compelling example of how structure, context, and perception interact to shape meaning. Though ostensibly devoid of inherent definition, its connotations span encryption, abstraction, technological sophistication, and exclusivity. Through linguistic exegesis and practical evaluation, it becomes clear that the significance of Cbybxrf does not lie in fixed semantics but in adaptive interpretation.
In real life, constructs like Cbybxrf underpin systems of cybersecurity, artificial intelligence, academic modeling, and organizational confidentiality. Their value derives not from aesthetic appeal but from functional precision and contextual control. By understanding how such terms operate, we better understand how language itself evolves—negotiated continuously between intention and interpretation.
Ultimately, Cbybxrf reminds us that meaning is rarely inherent. It is constructed, assigned, and reinforced through human engagement.
